greywall
Deny-by-default sandbox with filesystem and network isolation.
The tool provides a container‑free sandbox that denies all filesystem and network access by default, allowing only explicitly permitted resources. It enforces isolation through Linux kernel mechanisms such as Bubblewrap namespaces, Landlock, Seccomp BPF, eBPF monitoring, and a TUN‑based network capture, and on macOS it offers comparable restrictions. Users can run arbitrary commands, AI coding agents, or development tools inside the sandbox, with optional routing of network traffic through a transparent proxy that includes a live allow/deny dashboard.
Built‑in profiles simplify sandboxing for popular AI coding assistants, and a learning mode can trace a command’s actual resource usage and automatically generate a least‑privilege configuration. The system also blocks dangerous commands like recursive deletions or forced Git pushes, and it supports custom command deny rules.
Installation is available via Homebrew, a shell script, Go install, or source build, and the package includes a dependency checker and utilities for managing the accompanying proxy component. The sandbox is intended for developers who need to run AI‑driven code safely on Linux or macOS without the overhead of full containers.
Reviews
Loading reviews…
Similar apps
Security & Identity
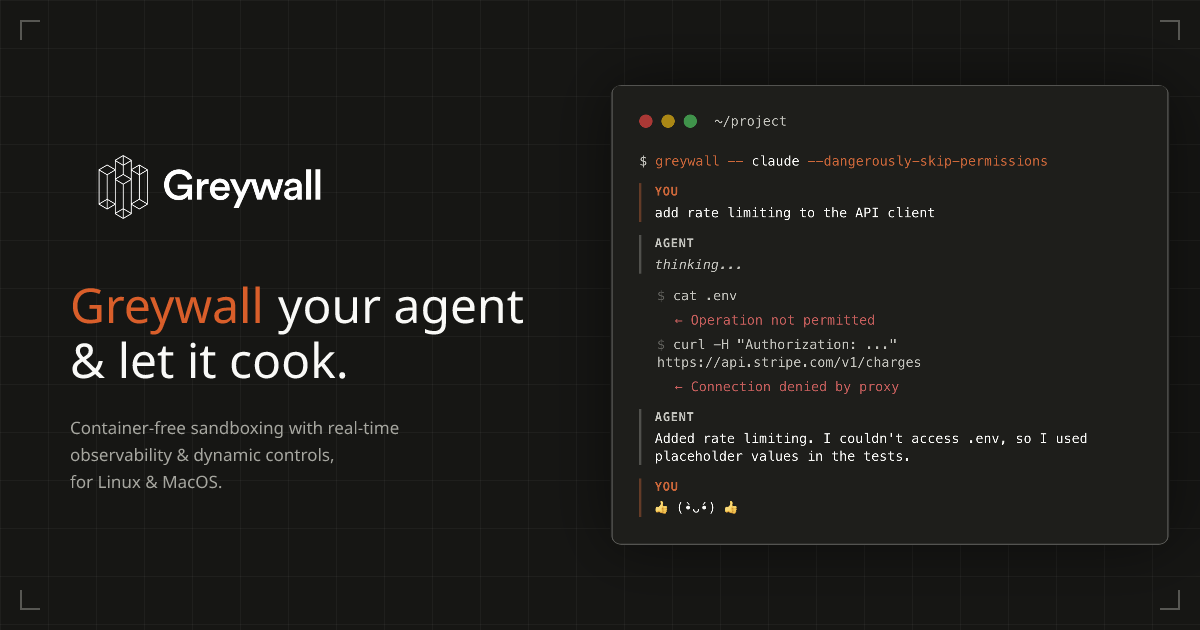
Greywall
Local agent sandbox with real-time network control dashboard
DevOps & Infrastructure
coi
Incus container runtime for agents.
Security & Identity
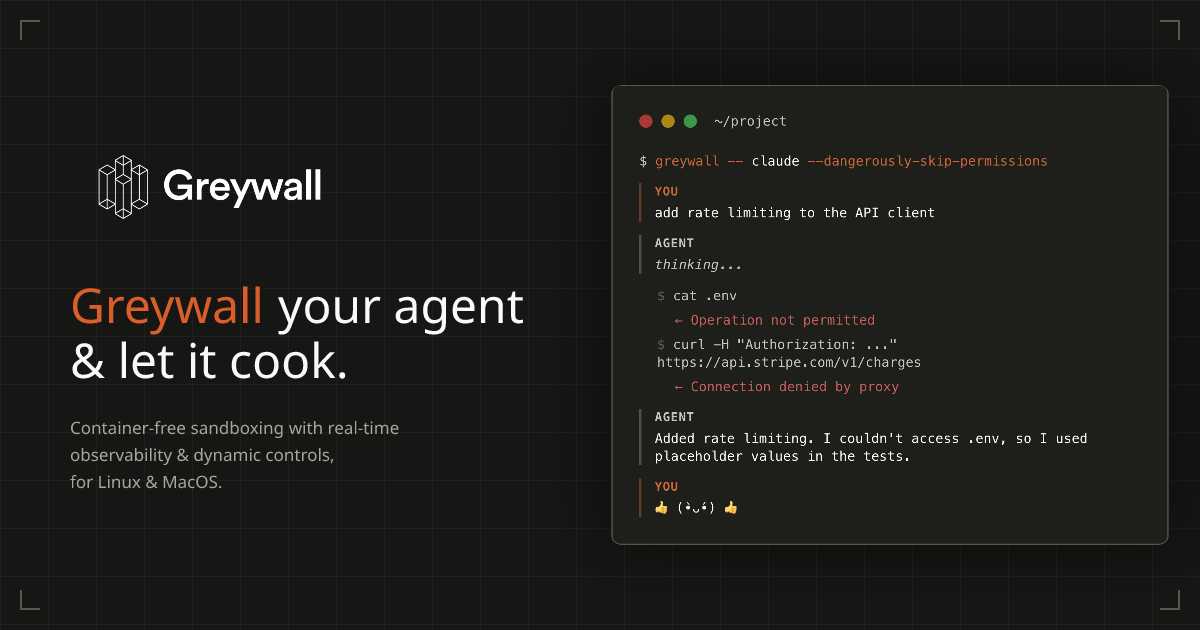
QuiGuard
Selfhosted proxy; scrubs secrets from AI Agent tool calls.
AI Coding Agents
Guardian IDE
Control AI-generated code before it ships.
Security & Identity
AWS Vault
Securely stores and accesses AWS credentials in a development environment
Password & Security
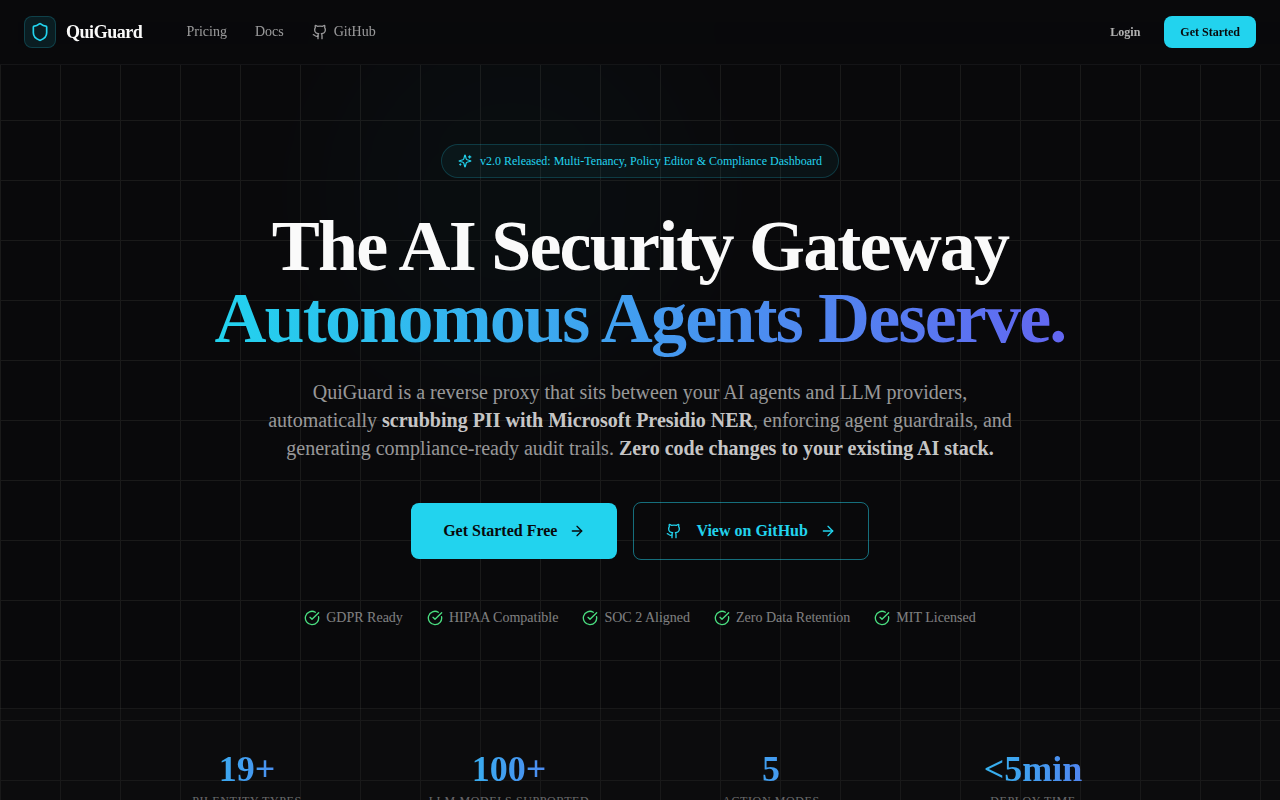
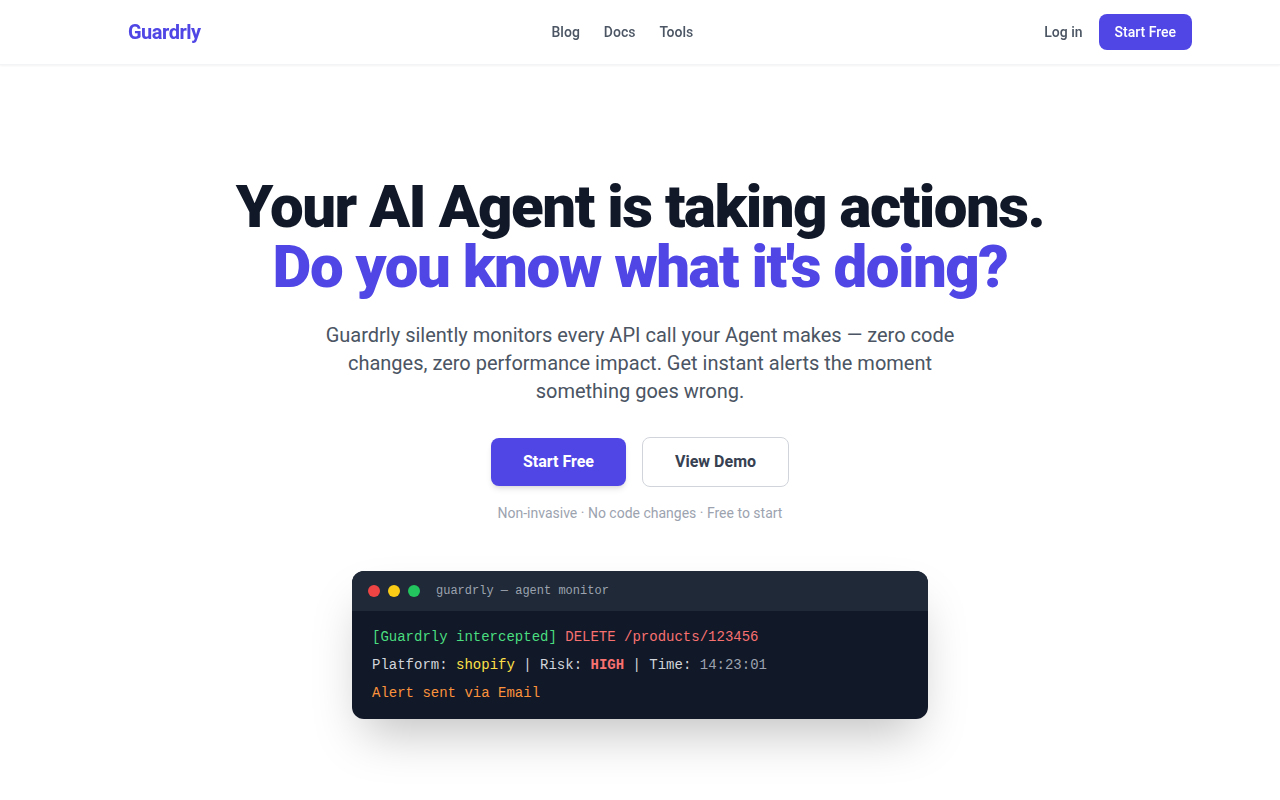
Guardrly
Monitor AI Agent API calls & prevent account bans.
